The defence industry is turning to a new generation of systems for faster, cheaper and more flexible communication, security and more.
Communication is essential for military operations, although it is difficult to establish in many cases. Laying cables, deploying equipment and securing connections is time consuming, inflexible and limits users’ mobility. Network deployment speed can be increased by using wireless technologies. These help military staff and commanders to stay connected and provide flexibility to move freely. However, a more connected world that integrates the Internet of Things (IoT), Cloud computing and advanced wireless communication also invites new kinds of threats. Network security is no longer just about protecting equipment and borders. Attacks now aim at security gaps in aircraft, sensors, satellites and space vehicles.
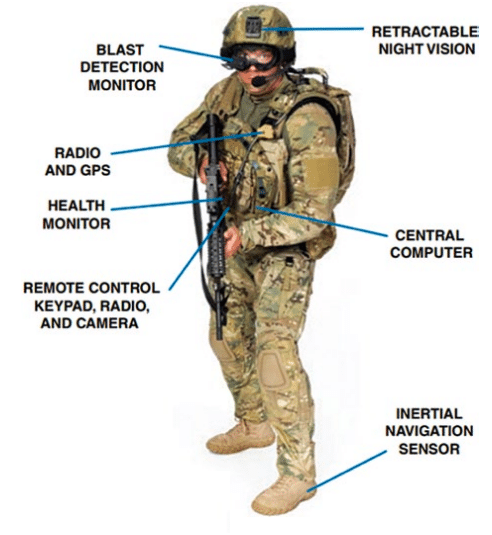
In military applications, vast amounts of data flow through sensors. This requires a single data stream that can combine video feeds from drones targeting radars and mobile phone intercepts. With reduced weight, size and power consumption, it has become easier to integrate more sensors into soldier systems. Within the defence world, information needs to be communicated in a wireless way, from sensors to war fighters.
Nitin Shetty, chief executive officer, Convergent Technologies, says, “We provide two solutions for wireless communication for defence: local and remote spectrum monitoring and surveillance systems, and Global Positioning System (GPS) protection against spoofing and jamming threats.”
He adds that, assured access and awareness of radio frequency (RF) spectrum are critical for a wide range of military and security applications. There are critical national infrastructures that rely on GPS-delivered positions, navigation and timing for daily operations. There is a need to protect these installations.
Convergent Technologies provides solutions for regulatory monitoring and management, finding direction and geolocation of emitters, technical surveillance countermeasures, remote sites, and perimeter and border monitoring, among others. They provide protection against the vulnerability of GPS systems to various signal incidents. Their solutions are better and secure as they provide full turnkey spectrum monitoring and management solutions and in-country support and service.
They provide indoor, outdoor, portable and IP67-compliant solutions that are based on a programmable anomaly detector that validates GPS sub-frames for spoofing incidents. Further, new validation rules are dynamically loaded as new threats are identified. There is also input capability from an atomic clock reference that enables users to enhance the holdover performance for accurate time.
Girish Baliga, marketing manager, Keysight Technologies India Pvt Ltd, says, “Keysight is a leading solution provider to the aerospace and defence sector for Internet, wireless communication, satellites, space and navigation, radar, electronic warfare systems and signal intelligence. Radar and satellite communication systems require higher frequencies, larger bandwidths and greater sensitivity to support uninterrupted connections.”
In network-centric warfare, both speed of information sharing and quality of information form an integral part of the information domain. This is where the choice ofcommunication technology plays an important role.
Commercial mobile communication technologies were limited in terms of data rates, bandwidths, intellectual property (IP) connectivity, etc. These limitations are being addressed by continuous enhancements in the 4th generation of mobile technology, Long Term Evolution (LTE). In release 12 of 3GPP LTE standards, enhancements specific to public safety and mission-critical applications, have been identified, and these have taken shape in the latest release 14 of 3GPP LTE standards.
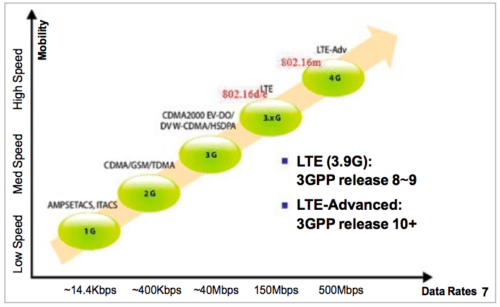
Asish Jain, application engineer, Keysight Technologies India Pvt Ltd, says, “LTE offers multiple deployment bandwidths, namely, 1.4MHz, 3MHz, 5MHz, 10MHz, 15MHz and 20MHz, giving the option for flexible choice depending on the application. LTE being an all-IP technology offers high level of security as desired for defence applications. One of the most important aspects of LTE in this regard is orthogonal frequency division multiplexing (OFDM) and orthogonal frequency division multiple access (OFDMA).
“OFDM has been the backbone of current commercial wireless systems because it delivers high data throughput in real-world environments, along with spectral efficiency and link flexibility. OFDM’s low symbol rate and multicarrier structure, combined with coding and forward error correction, allow it to operate effectively in channel conditions degraded by interference, jamming and frequency selective fading.”
Because of its multicarrier structure, OFDM is readily extendable to simultaneous multiple access capabilities by mapping subcarriers to users in a scheme called OFDMA . This multiple-access approach is especially attractive because multiple users can be supported in a flexible fashion with only minor changes in air interface.
In addition, multiple-input multiple-output (MIMO) techniques can be used with OFDM and OFDMA systems to further improve data throughput in the presence of multipath environments.
These underlying benefits of LTE make it attractive for flexible deployment in both terrestrial and marine defence applications. One important element of network-centric warfare is video streaming for improved situational awareness. Defence users could potentially take advantage of sophisticated existing hardware and software solutions that offer proven commercial performance in different physical environments from wide open terrain to complex and obstructed urban environments.
Secure and reliable connectivity in military networks is crucial as vehicles, sensors and soldiers become increasingly connected for improved situational awareness and communication. Manoeuver command, control, communications and intelligence depend critically on these networks to improve troop agility and advantage in battlefield situations.
Field communication modules such as soldier-borne radio communications and software-defined radio (SDR) based data links are often signal-processing intensive, power constrained, have stringent security requirements and are also jam resistant. Real-time situational awareness, threat detection and signal intelligence are also required in defence communication.





Sir , I want to know which project is better sensor in soldiers system or sensors applied on the border?