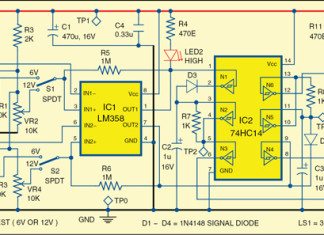
Monitor for 6V/12V Batteries
Rechargeable batteries of 6V and 12V are used in a large number of applications. It is imperative that these are maintained properly to get...
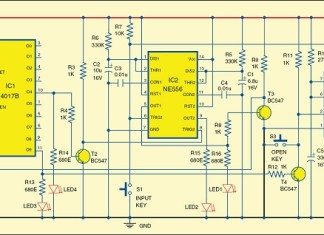
Laser Based Security Lock
Presented here is a security system that uses an inexpensive laser torch which is usually available with a key ring. The advantage of this...
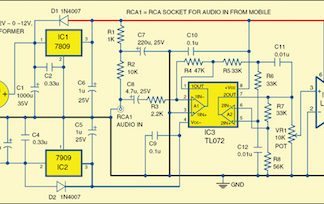
Simple Low-Power Audio Amplifier
The small-signal amplifier is generally referred to as a voltage amplifier because it usually converts a small input voltage into a much larger output...
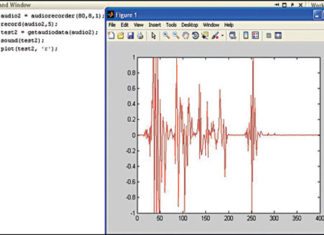
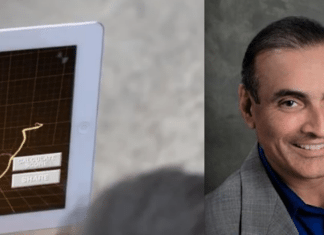
Plotting with MATLAB
MATLAB is a useful software tool for engineering and computational mathematics. It also plays a very important role in scientific and engineering plots. This...
Part 2 of 2: How to Ensure E-mail Security
E-mail authentication has become a big problem and many methods are being incorporated by e-mail servers across the world to overcome this problem. There...
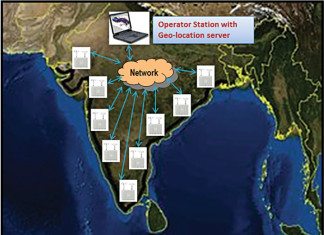
RF Surveillance: A Case of Homeland and Border Security
Although security threat can emerge from many sources, the one which is really brutal and catastrophic is terrorism. Terrorism has far reaching consequences like...
“Bluetooth Smart offers rapid rollout of low-power consumer products around the...
The IoT requires almost all objects to have some communication ability built into them. What is the scope of Bluetooth Smart in the IoT...
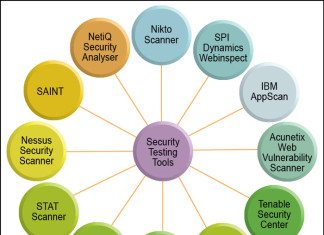
Security Testing Tools: Wapiti, OWASP ZAP and Netsparker—A Comparison
Before digging into the details of web application security testing, let us first take a brief overview of application security testing. Security testing can...
Value Additions by Component Distributors
An enterprise exists in eternal pursuit of maximising profits. Electronics industry is no exception. And perhaps it exists in most dynamic environment, be it...
Tackling Power Consumption With High Technology
We have all heard of many software and hardware techniques to reduce power consumption. This interview takes a look at two impressive technologies that...