Although the Internet of Things (IoT) is one of today’s hot marketing buzzwords, most engineers have long known that there are significant benefits in adding connectivity to almost any electronic device. IoT is therefore a very broad term, covering a huge range of applications, from moving security cameras from CCTV to IP connectivity and connecting sensors in factories to wearable fitness trackers and remote control of the heating for your home.
One challenge that faces all developers of internet-connected devices is security. Why is security such a concern for IoT? The unprecedented volume of data that is available, the level of interconnectivity between all IoT systems and the potential for harm drive much of the perception of risk. One factor that should not be underestimated is the proportion of engineers who previously developed systems that were not connected to the internet who now must develop connected products.
Fortunately, suppliers, from semiconductor companies to distributors, are providing the technology and support that will enable the development of more secure IoT products, provided that engineers take the time to follow some basic principles.
Risks and Threats
The security risks associated with IoT are obvious when one considers the impact of failure of some of the systems that are connected to the internet. While major infrastructure and other safety-critical systems will have experts considering how to secure the systems and large security budgets, even something as simple and cost-sensitive as home heating systems must be secured.
At a recent meeting in Chicago, Roman Budek of NXP asserted that there are six primary security risks that designers of IoT systems must consider and address. Where data or control of the system is in the cloud, remote attacks on a cloud service providers must be considered: it is not sufficient to assume that choosing a major service provider will address this threat.
The nature of IoT means devices are often accessible, and physical attacks on peripheral systems, for example using a side channel to control a door lock, are a risk for many systems. Equally a vulnerable, counterfeit or compromised device could undermine the security of a network from the inside. This is a particular challenge as many IoT vendors believe that interoperability with other company’s products is important to ensure commercial success.
The gateway or IP edge node presents an opportunity for remote attacks. In the case of home automation, frequently the gateway is a low-cost router supplied by the customer’s ISP, which may have limited functionality and could have unpatched vulnerabilities.
Smart phones, tablets and watches present a risk as users might be persuaded to download a rogue app that would then have access to the network. Alternatively, PIN code phishing could give access to a device that has an app with access to the IoT system. Finally, as IoT matures and devices are replaced with newer products, decommissioned devices could be used as Trojan horses to compromise other network devices.
It’s clear that when designing IoT devices, engineers must take a holistic view of the whole system, and not just focus on the product they are designing.
Ensuring Security of Embedded Devices
When developing an embedded IoT device, engineers must ensure three things are achieved:
• Data Integrity: ensuring that data is protected from snooping and is only accessed by people authorised to do so, as well as making sure that the data cannot be changed to introduce either malicious or accidental errors.
• Code Integrity: securing the code is also critical. Changes to code must be detected, and only authorised changes allowed. Additionally, most companies are also concerned about protection of their intellectual property, requiring measures to prevent theft of the code
• Device integrity: it’s important to ensure that connected devices are authentic and their critical functionality has not been tampered with. IoT devices therefore need strong authentication and protection of cryptographic keys to prevent hacking and product counterfeits
To achieve this, security experts often refer to the six tenets of embedded IoT security that should underpin the approach of any developer: identity/authentication, authorization, audit, confidentiality, integrity and availability. At the heart of many of these tenets is cryptography.
Device Support for IoT Security
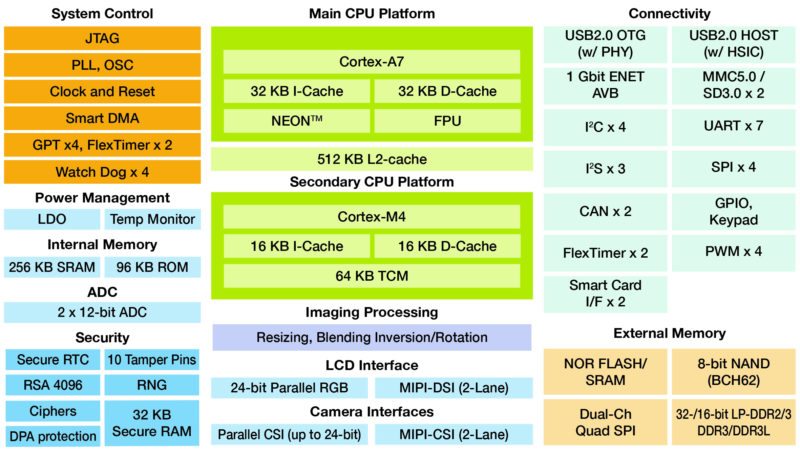
The good news for developers of IoT products is that many devices already provide support that makes it easier to build in security. Take the NXP iMX 7Solo applications processor that is used on the NXP WaRP7 IoT and Wearable Development Platform, which was developed in partnership with Premier Farnell. This IoT prototyping platform includes many security features that have been built into the processor.
One of the most obvious features is the support for encryption. The processor also includes support for hardware-accelerated encryption with the CAAM (cryptographic acceleration and assurance module). This module contains cryptographic and hash engines that support a wide range of cryptographic standards.
There are two basic types of cryptographic algorithm: symmetric and asymmetric, and choosing the right type of algorithm is an important decision in IoT system design.
Symmetric algorithms use the same key to both encrypt and decrypt the data, and require less processing overhead. Some of the most popular encryption algorithms, such as AES, which is very popular because it has never been reported as being hacked, use symmetric encryption. Although the algorithm is strong, the use of one secret key is a potential vulnerability, as it can be difficult to distribute and protect. Typically, symmetric encryption might use a key from 128 to 256 bits long.
Asymmetric encryption uses a “one-way” approach, with a pair of keys. A private key is kept secret and not distributed, while a public key can be shared widely. If the public key is used to encrypt, the private key is needed to decode, and vice-versa when the private key encrypts. This approach makes the system easier to manage and much more scalable. Furthermore, keys of up to 4096 bits can be used. The WaRP7 processor for example, includes support for these long, secure keys.
One requirement for encryption algorithms is the random number generator (RNG). This is used to generate the keys, which must be random to prevent a hacker from predicting the numbers and breaking the cypher. The CAAM offers National Institute of Standards and Technology (NIST) certified pseudo and true random number generators.
By providing hardware support on-chip, IoT devices can be developed that ensure a greater level of security by using stronger encryption without dramatically impacting on the processor’s capacity to run the application.
Despite the security of the algorithms available, it’s possible to use attacks that measure device power consumption to determine secret keys. This can be much easier than it sounds, as the cryptographic algorithms can involve rotating registers that contain the keys. The processor used on the WaRP7 board, however, includes countermeasures to prevent detection of keys by using simple (SPA) or differential power analysis (DPA).
IoT security is also enhanced by other features that are included on the processor used in the WaRP7, as well as some other processors. Secure non-volatile storage (SNVS) is hardware that determines whether the device is in a secure state, which in turn determines whether its resources can be accessed. When in a secure state, special cryptographic keys can be used to decrypt long-term secrets, such as public/private keypairs, DRM keys or proprietary software.
A security violation can be trigged by JTAG events, power glitches, Master Key ECC check failure, software-reported issues and hardware reported tampering using the tamper pins. When such as violation is identified, the system activates security-related hardware or software. In the case of highly sensitive applications, the tamper detect pins could trigger the hardware that will automatically and immediately erase the Zeroizable Master Key, denying access to and erasing the contents of the secure memory.
For some applications, real time clocks are a potential vulnerability. A simple example is electricity metering, where the clock could always be set to a time where the lowest rate is in force. Protecting the real-time counter using the same SNVS offers additional protection. With the WaRP7 board, engineers also have access to a monotonic counter, which cannot be reversed, protecting against “roll-back” attacks.
To ensure code integrity, processor vendors have introduced several approaches to isolate applications and ensure that the firmware of the system has not been compromised. The iMX 7Solo used in the WaRP7 includes two ARM cores that have TrustZone technology: ARM’s approach to identifying secure and non-secure worlds, blocking non-secure software from accessing secure resources directly. Effectively each physical processor has two virtual cores: one considered secure and the other non-secure.
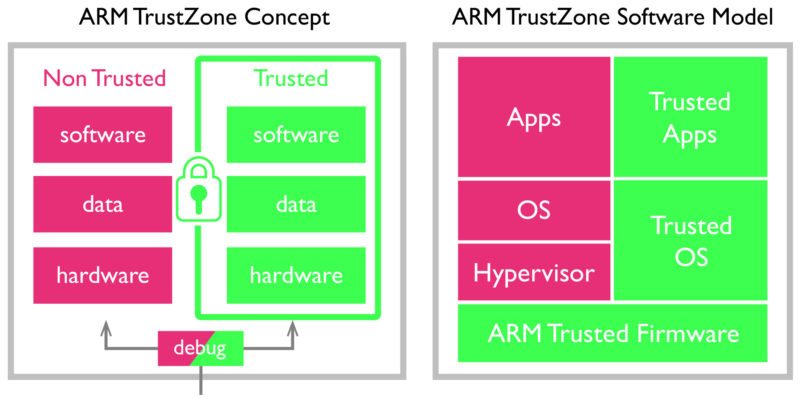
The TrustZone technology relies on secure low-level firmware. The inclusion of a high-assurance boot (HAB) feature, which uses digital signatures to recognise authentic software and prevent unauthorized software from gaining control of the boot sequence, ensures that this firmware cannot be compromised.
Dealing with the Complexity
This article has considered just one IoT board as an example of the features available to increase security. The challenge faced by engineers is the complexity that this introduces: the data sheet for the i.MX 7Solo family is 150 pages, and the reference manual runs to more than 4000 pages. Clearly help is needed to ensure that the time to learn about the features is not unrealistic.
Picking the right development platform in the first place is critical. Resources such as the element14 community’s Design Center provide detailed information about processors, development platforms, software tools and middleware. With applications engineers, also on-hand, distributors play a vital role in ensuring that the right selections are made, as well as reducing the learning curve with the appropriate tools and information.The very high levels of integration available today mean that development platforms often have just a few components, making them almost ideal hardware for production. Distributors works with many companies to customise existing boards such as the Raspberry Pi to meet their exact needs, or developing bespoke hardware to specific requirements, allowing more engineering resource to be applied to the code, where most of the complexity and much of the product differentiation will reside.
Conclusion – Security is one of the Biggest Challenges for IoT
Today almost every electronic device can benefit from connection to the internet, whether to allow remote control, monitoring or simply logging and analysis of data. The connection, however, creates many potential risks that must be addressed with appropriate security at the device and system level. With semiconductor and software vendors providing support for security features from encryption to physical security, there is now no excuse for IoT product developers who fail to build in security. Engineers, however, are faced with having to overcome the complexity that is inevitable with the additional functionality, and so they must look towards suppliers to help them meet these challenges.







Very interesting article. The greatest problem I’ve faced regarding security is finding the balance between a device with highly secure communication and a not so power hungry device. The protocol selection and components used to acoplish a secure encryption are the key, mainly in IOT design you can either go with a highly secure wifi communication or with a proprietary Lora of sigfox communication.