Although attacks against bitstream encryption have been known in the past, the latest discovery is perhaps the most harmful, given that it takes advantage of the reprogrammable feature of FPGA to perform remote data breach.
A field-programmable gate array (FPGA) is a user-configurable, programmable integrated circuit. It is a semiconductor device which contains an array of programmable logic blocks and interconnection circuits. It can be reprogrammed according to the required functionalities.
Besides being part of circuit boards used in applications such as aerospace and defence, consumer electronics, medical and automotive, FPGAs are a critical part of many security-related applications for cloud data centres, base stations and industrial control systems as well. Although these integrated circuits provide the flexibility of reconfiguration even after manufacturing, they do possess a hidden vulnerability feature as discovered in a joint research project conducted by scientists from the Horst Görtz Institute for IT Security at Ruhr-Universität Bochum and Max Planck Institute for Security and Privacy.
Called the “Starbleed”, this security bug gives attackers complete control over the FPGA chips and their functionalities. A bitstream or binary bits of information is central for the programming of FPGAs. In order to protect it adequately against attacks, the bitstream is secured by encryption methods. However, the researchers were successfully able to decrypt this protected bitstream, gaining access to the file content and modifying it.
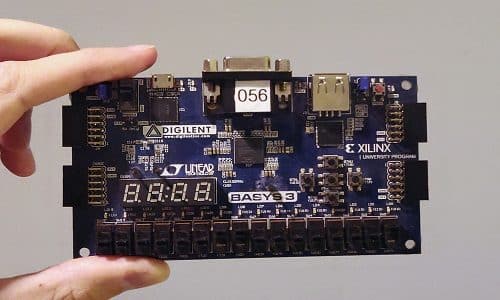
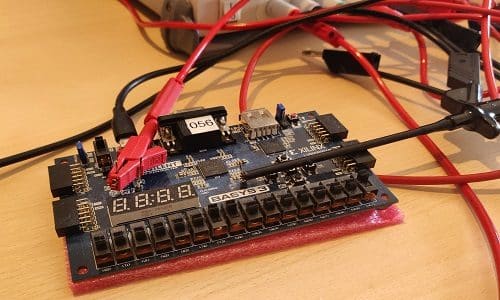
Testing out leading semiconductor brand
As part of their research, the scientists analysed FPGAs from Xilinx, one of the leaders in field-programmable gate arrays. To overcome the encryption, the research team exploited the reprogramming feature of FPGAs by manipulating the encrypted bitstream during the configuration process to redirect its decrypted content to the WBSTAR configuration register, which could be read out after a reset.
“If an attacker gains access to the bitstream, he also gains complete control over the FPGA. Intellectual properties included in the bitstream can be stolen. It is also possible to insert hardware Trojans into the FPGA by manipulating the bitstream,” said Christof Paar, professor at the Max Planck Institute for Cybersecurity and Privacy. “Although detailed knowledge is required, an attack can eventually be carried out remotely without having physical access to the FPGA.”
The Starbleed vulnerability was found to have affected Xilinx’s 7-series FPGAs with the four FPGA families Spartan, Artix, Kintex and Virtex as well as the previous version Virtex-6, which form a large part of Xilinx FPGAs used today. “We informed Xilinx about this vulnerability and subsequently worked closely together during the vulnerability disclosure process. Furthermore, it appears highly unlikely that this vulnerability will occur in the manufacturer’s latest series,” said Dr Amir Moradi, professor at the Horst Görtz Institute for IT Security at Ruhr-Universität Bochum.
Since the bug is integrated into the hardware of current FPGA chips, the best way to avert this security risk is to replace them with new versions that are free from Starbleed.
For more details read here.





