What if edge devices could secure and process data at the same time? A new hardware approach does both, reducing energy use and removing separate security layers.
A cross-institutional research team has developed Co-Located Authentication and Processing (CLAP), a system that protects data while maintaining performance in edge devices. The work brings together researchers from multiple institutions and focuses on solving the trade-off between security and speed in edge computing.
CLAP combines authentication and data processing on a single memristor-based platform. It is designed for edge devices such as wearable medical systems and industrial IoT units, where both protection and efficiency are required.
Edge devices handle sensitive data but operate under tight limits of power and hardware. This creates a challenge: ensuring strong security without reducing performance. Past incidents have shown that attackers can exploit such systems, including remotely altering insulin delivery or accessing vulnerabilities in cardiac devices. These cases show the need for built-in security in systems where resources are limited.
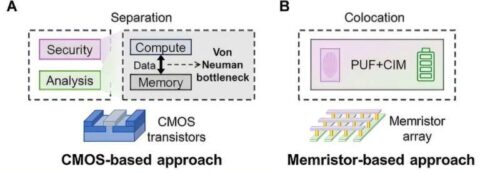
The system is built around memristors, components that can store data and perform computation in the same place. This removes the need to move data between memory and processing units, which is common in conventional architectures. Memristors also show small physical variations from one device to another. These variations act as unique identifiers, enabling device authentication while the same hardware performs computation.
By combining these two properties, CLAP removes the need for separate modules for security and data processing. This reduces hardware complexity and energy use while maintaining both authentication reliability and computational accuracy.
The system has been tested on multiple tasks, including discrete wavelet transform, discrete Fourier transform, compressed sensing, and neural network operations. In one example, it was used for secure electrocardiogram data collection. The system achieved high authentication accuracy and efficient signal compression. It also showed improvements in energy efficiency and chip area compared to conventional designs.
This approach shows a shift in edge computing design, where security is built into the hardware rather than added as a separate function.