Algo Engines interfaces with hundreds of different sensors, supervisory control and data acquisition (SCADA) systems and smart metres, and pulls information collected by them to the cloud, analyses this massive and complex data using IBM tools for better predictive maintenance and forecast. A web based platform is made available to the customer where they can gauge the health of the device, monitor its performance, and view forecasts and predictions of component failure. These factors further increase the efficiency, effectiveness and, hence, revenue of the system.
Life-sciences and medicine
Big Data analysis in IoT networks is taking the idiom ‘prevention is better than cure’ to a whole new level. Advanced sensors, mobile apps and extensive databases are helping us reach the goal of personal health improvement.

Converting thoughts into actions. Brain-computer interface (BCI), also known as brain-machine interface (BMI) or mind-machine interface (MMI) or direct neural interface, is a method that conjoins the human brain and machines, and lets you control external devices like bionic modules using your thoughts. The system consists of several powerful and precise sensors (typically multi-electrode arrays) that collect brain signals, a decoder that can detect and interpret neural signals related to each activity, and an external module like a computer screen or robotic arm that translates these electronic signals into corresponding actions. This technology is a breakthrough in the field of medicine as it can help restore disabilities of patients, and institutions like BrainGate and Pitt School of Medicine (University of Pittsburgh) are putting in a lot of research in this field.
From existing to next-gen intelligent system
Converting from an old-fashioned system to a next-generation intelligent connected system is going to be a major problem when adopting the IoT on a larger scale, and a lot depends on what the user already has in hand. Over a period of time, even without us realising, we are already upgrading the infrastructure. These are invisible upgrades. An example is the wireless network that started with no wireless communication and moved to 1G, 2G and 3G, and then to 4G LTE and WiMAX.
In some cases, it requires partial or complete replacement of hardware. These are visible upgrades, like sensors or Wi-Fi-enabled bulbs. Many systems and protocols these days make it very easy to add an IoT component to the existing device. For example, systems based on highway addressable remote transducer (HART) protocol can be easily upgraded to WirelessHART, by using an adapter and a gateway. “But, sometimes the cost or effort required to backward-integrate can be so high that it would be advisable to replace the existing equipment with a new system altogether,” says Nihal Kashinath of IoTBLR.
Is IoT security a catastrophe waiting to happen
Any communication that happens over-the-air needs to be secure. But, functionality and safety are found to be interdependent. Increasing the functionality will dilute the safety, as entrepreneurs focus their time, effort and resources on developing better features. In a similar way, giving more focus on security hampers functionality. The challenge is to strike the right balance between these aspects, and this becomes the deciding factor for long-term success of any system.
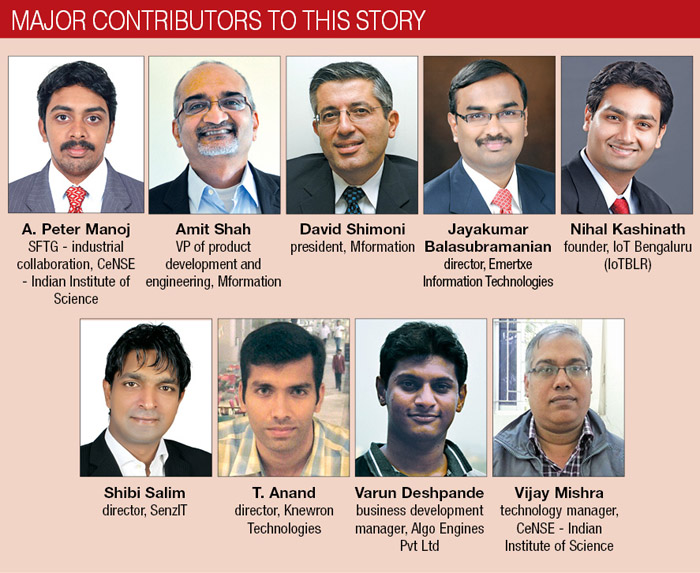
Nihal Kashinath says that current IoT systems are not very secure because there is a lack of seriousness about security, given that attacks on connected devices have been sporadic. This is dangerous, since security should be in the fabric of the connected-devices system, not as a separate module that is tacked on later.
However, T. Anand believes that, as of today, systems are secure enough. In the long run, the design and architecture of these systems or applications would tell more. Cases of network security attacks are very few, considering the number of connected devices available these days, observes Shibi Salim. Developers are becoming more vigilant and focussing well on security aspects.
“When it comes to data and bearer security, it is all managed by very well-defined standards and protocols,” says Amit Shah. This is a multi-layered approach. Security of data that we are sending on the cloud has multiple layers—social security number (SSN), username and password—and, a lot of sensitive data is obfuscated or made anonymous, so that even if you get hold of it, you cannot make sense of it.
Then comes security of access—who can get hold of the data. When access is secured, data is segregated and controlled by a unique identifier, so one person cannot get hold of another person’s data.
Many people are too intimidated by the idea of companies or people getting access to data that they might not want to share with them. Some examples are the positioning data Google receives through Maps app or the use of phones to take photos in high-security regions, thus losing privacy in the digital world.
To solve such issues, there are solutions like geo-fencing that allow you to switch-off your device completely, switch to flight mode or disable certain functions when inside a virtually-defined location, thus protecting real-world privacy.
From inflated expectations to the plateau of productivity
Gartner’s hype cycle report might have the IoT as its most over-hyped technology in 2014, but their analysts believe that it will only take five to ten years for it to reach maturity, or the plateau of productivity, according to the hype cycle. Coincidentally, the prediction for Big Data reaching the same level of maturity is also five to ten years. The year 2025 sure looks set to be an extremely promising year for us technologists.
Dilin ANand is a senior assistant editor at EFY.
Anagha P is a dancer, karaoke aficionado, and a technical correspondent at EFY. Find her on Twitter @AnuBomb.




